Cyber threats are evolving fast, and if you think your business is too small to be a target, think again. Over 50% of small businesses have experienced a data breach or cyber attack, and the sophistication of these attacks only keeps climbing. No company is immune, from lean startups to global corporations. The good news is that with the right measures in place, you can protect your sensitive information and keep your operations running without interruption. (Source: AdvisorSmith, getastra.com)
Table of contents
- Train your staff
- Keep Your Software And Systems Updated
- Ensure Endpoint Protection
- Install a Firewall
- Deploy AI Means In Your Cybersecurity Strategy
- Encrypt Your Data and Create Backups
- Control Access To Your Systems
- Implement WiFi Security Measures
- Partner With Experienced Cybersecurity Consulting Firms
- Create Secured Employee Accounts
- Always Use Strong Passwords & 2-Factor Authentication
- Assess and Monitor Third Party Vendors
- Invest In Security Solutions & Tools

Train your staff
Your employees are your first line of defense, and they can also be your biggest vulnerability. Educating your team on how to spot and respond to threats is one of the most effective steps you can take. Regular training sessions keep your staff sharp, aware of the latest tactics cybercriminals use, and confident in knowing exactly what to do when something looks off.
According to EY’s cybersecurity research, only 36% of CISOs are satisfied with how well non-IT staff adopt cyber best practices. That gap is a real problem, and it points to the need for smarter, more engaging training approaches. Start by teaching your team to pause before clicking any link in an email. They should check the URL carefully and confirm it’s legitimate before going further. The same goes for email addresses. Cybercriminals are skilled at crafting addresses that look almost identical to the real thing, so attention to the smallest detail matters. When an unusual request lands in someone’s inbox, especially one involving sensitive data, train your people not to just comply. Encourage them to verify through a separate channel, like a quick phone call to the supposed sender. Beyond training, pair these habits with strong technical measures. Think robust passwords, two-factor authentication, regular software updates, and dependable antivirus and firewall protection.
Keep Your Software And Systems Updated
Keeping your software and systems current is one of the simplest and most powerful things you can do for your cybersecurity.
Updates do more than add new features. They patch security holes, fix bugs, and make your systems far harder for attackers to exploit. A well-updated system is a much less attractive target.
Outdated software is one of the most common entry points for hackers. They actively look for businesses running old versions, knowing those systems carry unpatched vulnerabilities. Once they’re in, the damage is already done and it’s often too late to act.
| Importance of Software Updates | Key Practices |
|---|---|
| Protects against cyber-threats | Enable automatic updates |
| Improves user satisfaction | Regularly check for updates |
| Enhances compatibility | Verify official update sources |
| Fixes vulnerabilities | Avoid unverified executable files |
| Reduces risks of data breaches | Watch for language errors |
Install a Patch Management Software
Think of a patch as a targeted update for a specific program already installed on your system. Rather than rewriting everything from scratch, a patch addresses a particular bug or weakness, keeping your software running smoothly and securely.
Patches can be applied across your entire network, covering servers, routers, operating systems, and more. Trying to track and apply all of these manually every day is simply not realistic for most businesses.
Patch Management software handles all of that for you. It scans for available patches, helps you decide which ones are necessary, and ensures they’re deployed correctly across your systems. It keeps everything tighter and more consistent without adding strain to your team.

Ensure Endpoint Protection
Endpoint protection is the cybersecurity approach focused on defending the devices connected to your network, think desktops, laptops, and mobile devices, from malicious activity.
Traditional firewalls alone are no longer enough, especially as remote work becomes the norm. Modern endpoint protection goes well beyond blocking viruses. It delivers robust malware defense and advanced cyber threat tactics tailored to today’s environment.
With BYOD policies and the rise of the Internet of Things, more devices than ever are connecting to your corporate network. Tablets, personal laptops, and smart devices are all easy targets for hackers looking for a way in.
Any device that connects to your corporate network from outside its firewall qualifies as an endpoint. The list includes laptops, smartphones, tablets, desktop computers, servers, and smart devices connected through IoT.
- Laptops
- Tablets
- Mobile devices
- Internet of things (IoT) devices
- Point-of-sale (POS) systems
- Switches
- Digital printers
- Other devices that communicate with the central network
If your business runs across multiple locations or has a large workforce, a centralized endpoint control system is worth your attention. These platforms use machine learning to detect new threats before they cause damage, prevent data loss, and come with built-in firewall capabilities.
How endpoint protection works
The traditional or legacy approach to endpoint security relies on an on-premises data center as the central hub. A management console connects to all endpoints and delivers security through locally installed agents. But because administrators can typically only manage devices within their perimeter, this model can create security silos that leave gaps in your coverage.
The shift to remote work exposed the real limitations of on-premises setups. As workforces spread across geographies, many endpoint protection vendors adapted by developing hybrid approaches, updating legacy designs to incorporate cloud capabilities without fully abandoning existing infrastructure.
The third approach is cloud-native, built from the ground up for a cloud environment. Administrators can monitor and manage all endpoints remotely through a centralized management console hosted in the cloud, connected to each device via a lightweight agent. That agent can operate independently too, keeping the endpoint secure even when an internet connection isn’t available.
Install a Firewall
A firewall is one of the foundational layers of any serious network security strategy. It acts as a gatekeeper, blocking malicious traffic before it ever reaches your systems. The real advantage is the level of control it gives you over what moves in and out of your network. Hardware firewalls are well suited to protecting large networks, while software firewalls let you fine-tune access at the individual application level.
Most firewall products come ready to deploy out of the box, which makes setup straightforward. But their default settings aren’t always the most secure. Regular updates and active monitoring are what actually keep your internet safety measures effective over time.
Steps to configure a firewall
- Step 1: Secure the firewall
- Step 2: Establish IP address structure and firewall zones
- Step 3: Configure Access Control Lists (ACLs)
- Step 4: Configure other firewall services and logging
- Step 5: Test the firewall configuration
A firewall works best when it’s part of a broader security approach. Pair it with antivirus software and smart browsing habits for stronger coverage. Next-generation firewalls take this even further, offering more tailored protection that adapts to your organization’s specific needs and threat profile.
That said, no firewall is a complete solution on its own. It should be one component of a well-rounded security plan, not the whole strategy.

Deploy AI In Your Cybersecurity Strategy
AI in cybersecurity means using artificial intelligence technologies to strengthen how you protect your digital systems and data. It draws on machine learning, neural networks, and other AI-driven techniques to detect, prevent, and respond to threats faster and more accurately than traditional methods allow.
One of AI’s biggest strengths is threat detection. It processes enormous volumes of data in real time, catching anomalies and potential threats that older methods would likely miss. And when a threat is detected, AI can automate certain incident responses, cutting the time between detection and mitigation and reducing the overall damage a cyberattack causes.
AI also enables a proactive defense posture through predictive analytics, helping you anticipate threats before they materialize. It makes sense of complex, multi-source data to give your team a comprehensive view of the threat environment. By automating routine tasks like monitoring, threat hunting, and incident response, AI frees your security team to focus on higher-level strategy. And because AI solutions scale with your operations and continuously learn from new threats, your defenses evolve alongside the risk. Understanding how digital security frameworks operate gives you a stronger foundation for knowing where AI fits in.
Leading Organizations Are Showing The Way
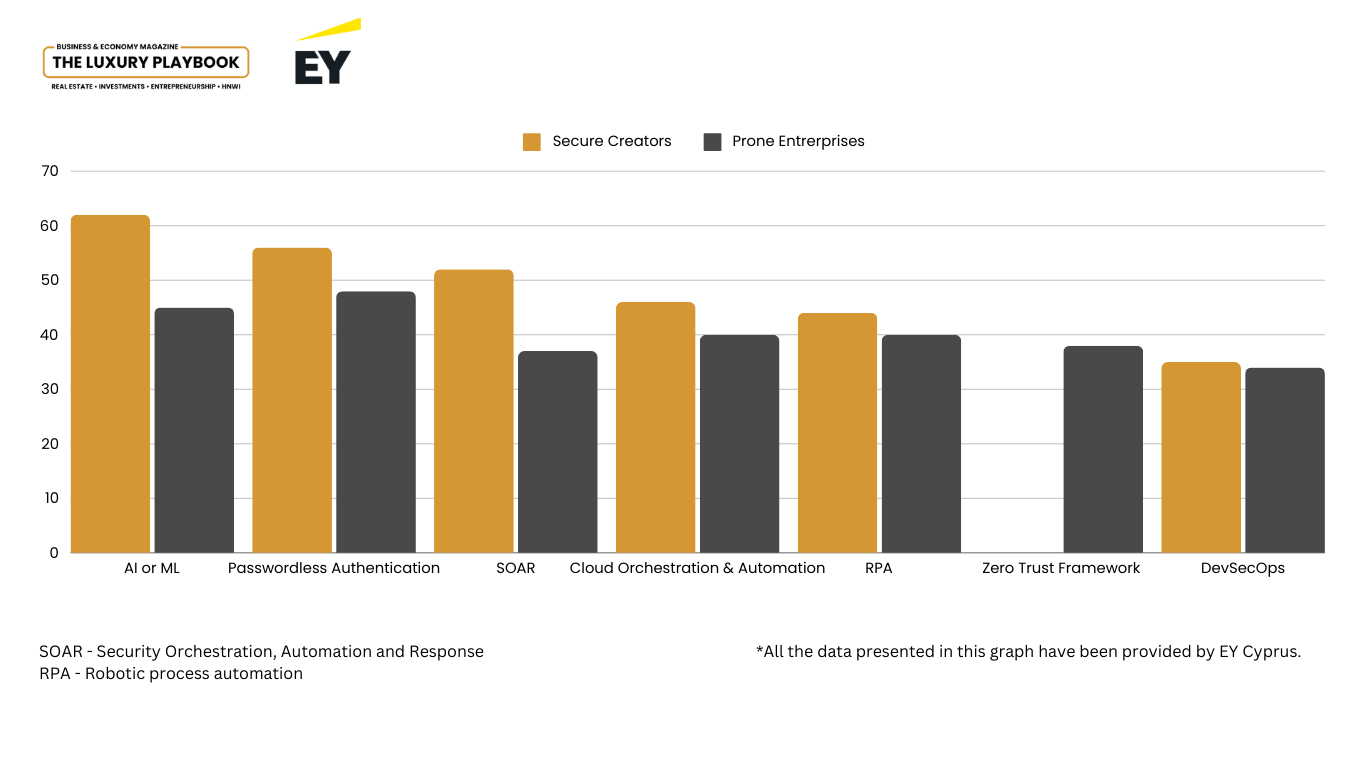
EY used statistical modeling to identify the organizations with the most effective cybersecurity postures, calling this group “Secure Creators.” Compared to their lower-performing counterparts, labeled “Prone Enterprises,” Secure Creators experience fewer cyber incidents and respond to threats significantly faster when they do occur.
The data is clear. Companies that have invested seriously in their cybersecurity strategies are the ones leading the charge on integrating AI and automation into their daily security operations.
Encrypt Your Data and Create Backups
Protecting your critical information through data encryption is non-negotiable for any serious business today. Research shows that over 93% of networks can be successfully breached, which makes advanced security measures not just useful but essential. (Source: PTSecurity)
When you encrypt your data, it stays protected even if someone gets past your other defenses. Backed-up data that’s also encrypted keeps your information private even if those backups are targeted. Encryption is what stands between your business and a hacker who has no key to unlock what they’ve stolen.
Encryption adoption across organizations is growing, and for good reason. It satisfies the requirements of major legal and compliance frameworks including GDPR, CCPA, and PCI DSS. Keeping your encryption keys stored separately from your backups adds an additional layer of control, ensuring only approved individuals can ever access the data.
Backing up your data consistently, whether daily or weekly, puts a hard limit on how much damage a successful attack can actually do. Well-managed encryption paired with frequent backups dramatically reduces the risk of permanent data loss, strengthens your privacy posture, and keeps your business running even when things go wrong.
Control Access To Your Systems
Breach volumes are projected to approach 15.4 million by 2026, a number that should make access control a top priority for any business serious about security. (Source: Secureframe)
Start by limiting system access to only the people who genuinely need it. Human error plays a role in 95% of breaches, and restricting access is one of the most direct ways to reduce that exposure. Keycards, biometrics, and other advanced identity solutions all play a part in building a comprehensive access control strategy.
Tightly managing administrative access is equally critical. When an employee leaves, revoke their passwords promptly and make sure all company assets are recovered without delay.
Over 80% of data breaches trace back to weak passwords, according to research from LastPass. The fix starts with requiring strong, individualized passwords for every employee account and enforcing multi-factor authentication across the board. Among internal breaches, 91% originate from phishing emails, which are often convincingly designed and easy to miss.
So educating your staff on how to recognize and report phishing attempts is not optional. It directly reduces the likelihood of a successful breach and adds a meaningful layer of protection to every account in your organization.
Implement WiFi Security Measures
Your business network is only as secure as the WiFi protecting it. Wireless security has come a long way since WEP launched in 1997, progressing through WPA in 2003 and then WPA2 in 2004, which remains the most widely used standard today.
For real protection, combine strong encryption protocols like WPA2 or WPA3 with firewalls and VPNs. When selecting a VPN, prioritize options with AES-256 encryption and trusted open-source standards. That combination gives you both security and privacy in one approach.
Your guest and employee networks should never share the same access point. Keeping them separate limits the risk of unauthorized entry and reduces the chance that a visitor’s device could compromise your internal systems.
Monitor and Analyze Network Traffic and User Activity
Monitoring your network traffic is one of the most effective ways to catch threats early. Unusual data flows, unexpected spikes, or odd connection patterns are often the first signs that something is wrong. Watching user activity adds another layer, helping you spot unauthorized access or behaviors that don’t fit normal patterns. Use wireless security tools that provide detailed audits through performance analysis, penetration testing, and packet inspection to keep everything visible and accountable.
These steps give you the ability to fix vulnerabilities before they become entry points, and that significantly reduces your exposure to a full-scale cyber assault.
Partner With Experienced Cybersecurity Consulting Firms
Most small businesses simply don’t have the internal resources to manage cybersecurity risks on their own. Partnering with an experienced cybersecurity consulting firm gives you access to advanced IT solutions and specialist knowledge that would take years to build internally. That expertise is what makes the difference when it comes to deploying strong cyber defenses and staying ahead of evolving threats.
A successful cyber breach can cause serious financial damage and lasting harm to your reputation. The case for working with cybersecurity professionals is straightforward. They protect your sensitive data, keep your operations intact, and give you confidence that your defenses are built by people who know exactly what they’re doing.
What cybersecurity consultants actually do spans a wide range of activities. Expect them to conduct risk evaluations, draft security policies, coordinate incident responses, and ensure your business stays compliant with the legal frameworks that apply to your sector.
On any given day, these professionals might be running security audits, building out defense strategies, overseeing security platforms, training your staff, managing regulatory compliance, or responding to an active crisis. It’s a demanding role that requires a rare combination of technical skill, analytical thinking, and clear communication.

Create Secured Employee Accounts
Securing your employee accounts is a cornerstone of any effective cybersecurity setup. It’s one of those areas where small oversights can lead to outsized consequences.
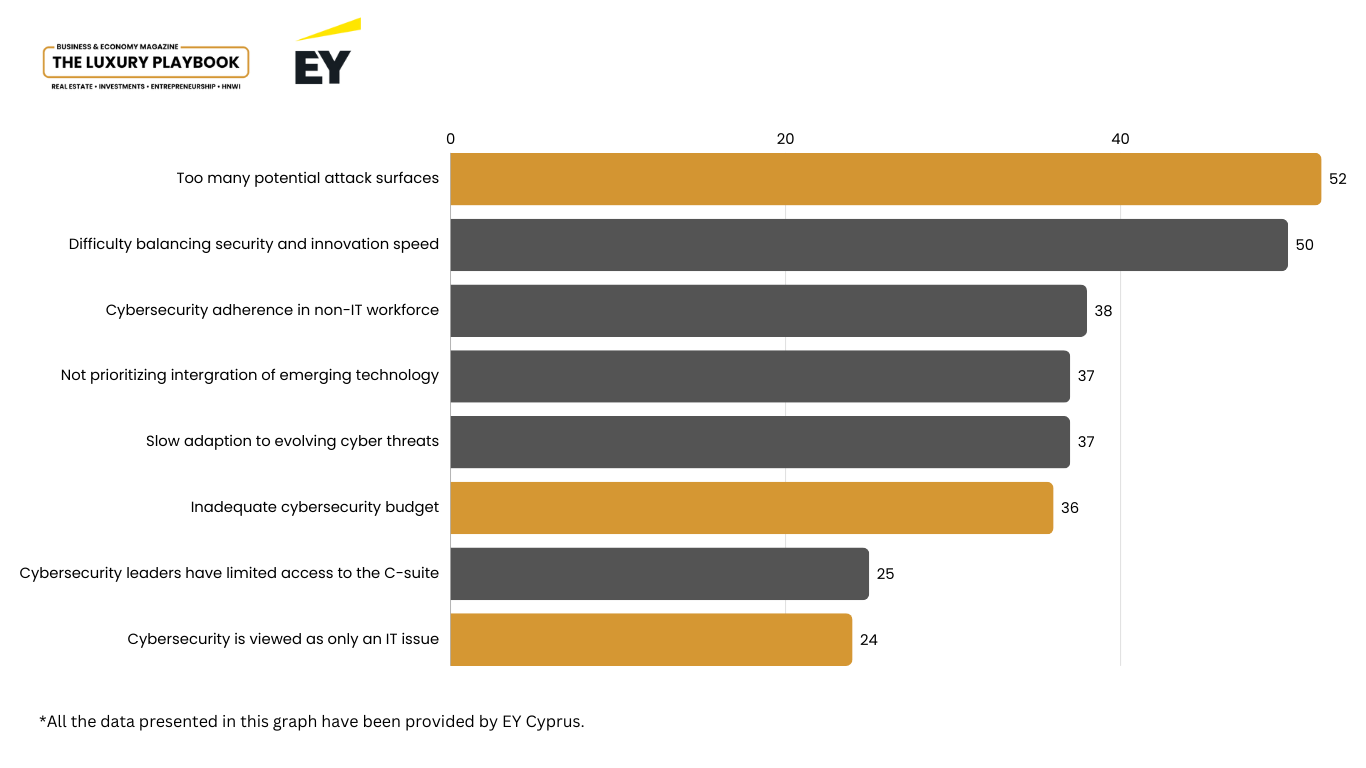
EY Cyprus data points to a consistent internal challenge across organizations, the sheer number of potential attack surfaces. Among the most exposed are employee accounts that haven’t been properly secured, making them an appealing target for anyone looking for a way into your systems.
How to Secure Your Employees’ Accounts
Start with strict password rules. When every employee uses a unique, hard-to-guess password for each account, you cut the chances of a breach dramatically. Generic or reused passwords are an open invitation, and tightening this one area can make a real difference across your entire organization.
Every step you take, whether it’s enforcing stronger password habits or running regular staff training, builds toward a more resilient cybersecurity posture. None of these actions work in isolation, but together they form a defense that’s genuinely difficult to penetrate.
Always Use Strong Passwords and 2-Factor Authentication
When it comes to fighting cybercrime, a strong password is your starting point, not your finish line. A solid password should be at least eight characters long and mix numbers, special symbols, and uppercase letters. But here’s the thing, research shows that even passwords up to 15 characters can fall short if the combinations aren’t complex enough. The bar is higher than most people think.
Adding two-factor authentication takes your digital defense to another level entirely. By requiring more than just a password to access an account, 2FA sharply reduces the chances of an unauthorized breach. It’s especially effective against phishing attacks, making it one of the most practical steps you can take to lock down account security.
Other tips worth knowing when it comes to passwords
- Unique Passwords: Refrain from using the same password for different accounts to lessen the impact of a security breach.
- Password Managers: Investing in a password manager can streamline the process of creating and storing complex and varied passwords.
- Password Updates: Changing your passwords regularly, ideally every few months, is imperative to continued security.
These habits protect individual accounts and strengthen your organization’s overall digital defenses at the same time. Keeping all software updated to close vulnerabilities is just as important, because even the strongest password won’t help if hackers find another way in through an unpatched system. Understanding how digital infrastructure is built can also give you a sharper perspective on where security gaps tend to appear.

Assess and Monitor Third Party Vendors
Your cybersecurity is only as strong as the weakest link in your supply chain. A thorough third-party risk assessment is one of the best ways to protect your critical company data. Build vendor monitoring into your broader cybersecurity plan, with the goal of identifying any risks a third party might introduce, drawing on both public and private data sources to watch for suspicious activity.
Evaluating media coverage and news is a key part of managing third-party risk effectively. Scan across sources for exposed credentials, negative press, or warning signs. Reviewing a vendor’s history of data breaches over recent years gives you a realistic picture of the risks they might bring to your business.
Ongoing vendor monitoring strengthens your overall cyber attack prevention strategy by helping you quantify and understand exactly where your third-party exposure sits.
A solid vendor management policy should cover, at a minimum, the core requirements for proper monitoring and vetting of any third party before they’re onboarded. This is what allows you to mitigate risk before it ever becomes a problem.
| Purpose and Scope | Define the purpose of the policy and its applicability within the organization. Specify the types of third parties that fall under the policy’s scope. |
| Roles and Responsibilities | Outline the roles and responsibilities of various stakeholders involved in the third-party risk management process, including risk owners, procurement teams, legal, compliance, and senior management. |
| Risk Identification | Establish criteria for identifying potential risks associated with third-party relationships. This could include financial stability, cybersecurity practices, compliance with laws and regulations, reputation, and operational resilience. |
| Risk Assessment and Classification | Provide a framework for assessing the identified risks, including qualitative and quantitative measures. Classify third parties based on the level of risk they pose to the organization. |
| Due Diligence | Detail the due diligence process that must be conducted before engaging with a third party. This may include background checks, financial audits, security assessments, and reviews of policies and procedures. |
| Risk Mitigation and Control | Describe the strategies and controls that will be implemented to mitigate identified risks. This could involve contract clauses, insurance requirements, security controls, and ongoing monitoring. |
| Contract Management | Include guidelines for contract negotiations that address risk-related terms and conditions, such as right to audit, data protection, and breach notification. |
| Ongoing Monitoring and Reporting | Define the procedures for continuous monitoring of third-party performance and risk exposure. Establish reporting mechanisms for risk-related incidents and changes in the third-party’s risk profile. |
| Incident Management and Contingency Planning | Provide a plan for responding to incidents involving third parties, including breach response and contingency plans for critical third-party failures. |
| Regulatory Compliance | Ensure the policy is aligned with relevant laws, regulations, and industry standards that govern third-party relationships. |
| Training and Awareness | Mandate training programs for employees involved in third-party risk management to ensure they understand the policy and their responsibilities. |
| Policy Review and Update | Specify the frequency and conditions under which the policy will be reviewed and updated to reflect changes in the organization’s risk appetite, the regulatory environment, and the business landscape. |
| Documentation and Record Keeping | Outline the requirements for documenting the risk assessment process, due diligence findings, and risk management actions. |
| Communication | Establish how the policy will be communicated to third parties and within the organization. |
| Escalation Procedures | Define the process for escalating high-risk findings to appropriate decision-makers within the organization. |
Invest In Security Solutions and Tools
Cyber threats don’t stand still, and your investment in cybersecurity tools needs to keep pace. Advanced solutions like AI-powered endpoint detection and response tools use behavioral analysis to identify and stop threats in real time. That kind of proactive capability saves your business significant time and resources compared to cleaning up after an attack.
Finding and fixing vulnerabilities within your own security systems is just as important as defending against external threats. Regular internal audits and penetration tests are how you stay one step ahead.
Regulatory compliance around data protection is mandatory across most industries, and falling short can result in heavy fines. By investing in comprehensive security software including intrusion detection and prevention systems, you satisfy those requirements while also building genuine trust with your customers. That trust is something worth protecting. For businesses operating across borders, understanding the intersection of compliance and financial structure is increasingly important.
If you’d like to connect with a cybersecurity advisor, you can reach out directly through the EY cybersecurity consulting page. Please note that this article is written for educational purposes only and should not be treated as tailored professional advice. Every situation is different, and your specific circumstances will always call for expert guidance.